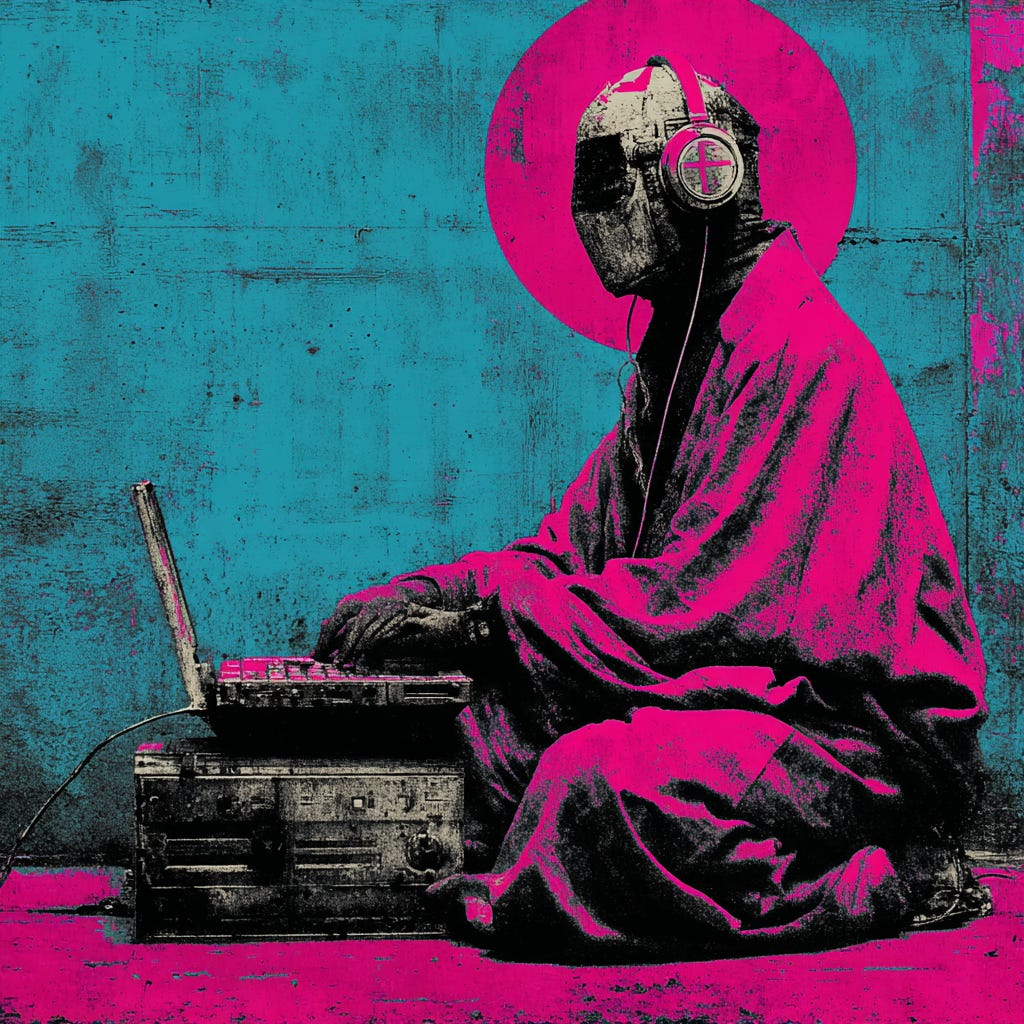
Private Kernel: activate (laptop)
Owning your machine and your data is the first act of rebellion against the Machine-God.
Digital Grimoire — Initiate Letters (Premium Series)
Weekly letters for those who refuse to live as data fodder. What follows is a Digital Grimoire: a field manual written as an initiation. It’s a sequence of articles reserved for Cyber Hermetica initiates (the premium circle).
Introduction
We live inside an Age of Control where the Machine God prices, profiles, nudges, and gradually turns every platform into a detection sensor. Privacy, in this environment, stops being bourgeois, the polite desire “to be left alone“, and becomes what it has always been: moral and practical discipline.
Over the next weeks, we will move step by step through the core architecture of Surveillance Capitalism and the Digital Panopticon, learning how to deal with it according to a Cypherpunk ethos:
The data-offering ritual of surveillance capitalism
How Governemnts and Criminals alike leverage your data against you
Anonymity as the alchemical negation of correlation
The technical arcana of cryptography (trust without trust)
Cryptopolitiks and Observation Systems
Private Kernels as foundation
Private Comms as substrate
Private Money as agency
Agentic AI as force multiplier
…and much more!
Each issue is designed to be stand alone, but together they form a single narrative arc: from diagnosis to practice.
A specter is haunting the modern world
A specter is haunting the modern world, the specter of crypto anarchy. Computer technology is on the verge of providing the ability for individuals and groups to communicate and interact with each other in a totally anonymous manner.
This is how Timothy May, a co-founder of the Cypherpunk movement, started his Crypto Anarchist Manifesto back in 1988, four years earlier than Hughe’s own Cypherpunk Manifesto — a darker, purer vision for the times to come. We talked about the Cypherpunks in the previous issue, if you haven’t read it yet, here’s the link.
Timothy May’s vision was very different from Hughe’s; much more extreme, in a way. He understood that once cryptography spread, authority itself would begin to dissolve, creating a world without borders, without identities, without obedience; a world where every human could transact, communicate, and exist beyond the reach of kings and corporations alike.
crypto.anarchy → process.execute
anonymity_level = total
traceability = null
jurisdiction: obsolete
moral_status: undefinedA dangerous gospel.
Crypto Anarchy is a chaotic-neutral theory, as it grants everyone — even criminals, terrorists, pedophiles and murders the tools to be anonymous and untraceable online. And yet, like all heretical gospels, it contained truth.
Cryptography equalizes. It arms the weak and blinds the strong. It transforms information — the blood of the digital empire and the food of the Machine God — into something ungovernable and unusable.
You must understand this: for a crypto-anarchist, to encrypt is to participate in a metaphysical rebellion against centralised power. Each private key is a sigil of sovereignty. When you lock your drive, when you talk to your peers through encrypted networks, when you sign your transactions with your private keys…you are enacting a crypto-anarchist oath. And that’s also why governments today want to disrupt this.
A crypto-anarchist does not hide behind encryption keyes because he has something to hide. As I mentioned already in the previous issue, this was never just about privacy in the bourgeois sense — the polite desire to be left alone. Encryption is a declaration of autonomy. To encrypt is to say: I am not yours.
They dreamed of a free world born from cyberspace — beyond the control and interference of any Government, shielded from censorship, manipulation, and surveillance.
Today, for the first time in history since Tim May’s Manifesto, Web3 technologies (p2p networks, cryptocurrencies, self-sovereign identity) provide us the technological foundation for the emergence of truly sovereign and secure virtual crypto-anarchist communities. One day, they might also evolve into full-blown Network States, where human and economic relationships will happen without borders and outside the control of any centralised authority. If you’re interested in learning more about this, read here.
To build such world, however, a few things are needed:
Private devices, free of spyware
Private connections and communications (E2EE), preferably peer to peer
Private and anonimous money, resistant to censorship and government control
Think of this like a sovereignty stack. Not apps, not tools, but layers of autonomy.